The Certified Kubernetes Security Specialist (CKS) path is one of the most practical ways to build real security skills for Kubernetes. It helps engineers and managers understand how to secure clusters, workloads, images, runtime, and access control in a hands-on way. DevOpsSchool’s CKS certification training page also highlights that the course is focused on securing Kubernetes environments and is designed for professionals such as Kubernetes administrators, cloud admins, security engineers, DevOps engineers, and SREs.This guide is written for working engineers and managers (India + global), especially software engineers who want to become more valuable in cloud-native teams. The goal is simple: help you understand what CKS is, who should take it, what you will learn, how to prepare, and what to do next.
Why Certified Kubernetes Security Specialist Matters Now
Kubernetes is powerful, but the attack surface is also large.
A team can have:
- weak RBAC permissions,
- exposed secrets,
- insecure container images,
- missing network policies,
- poor runtime monitoring,
- and no audit visibility.
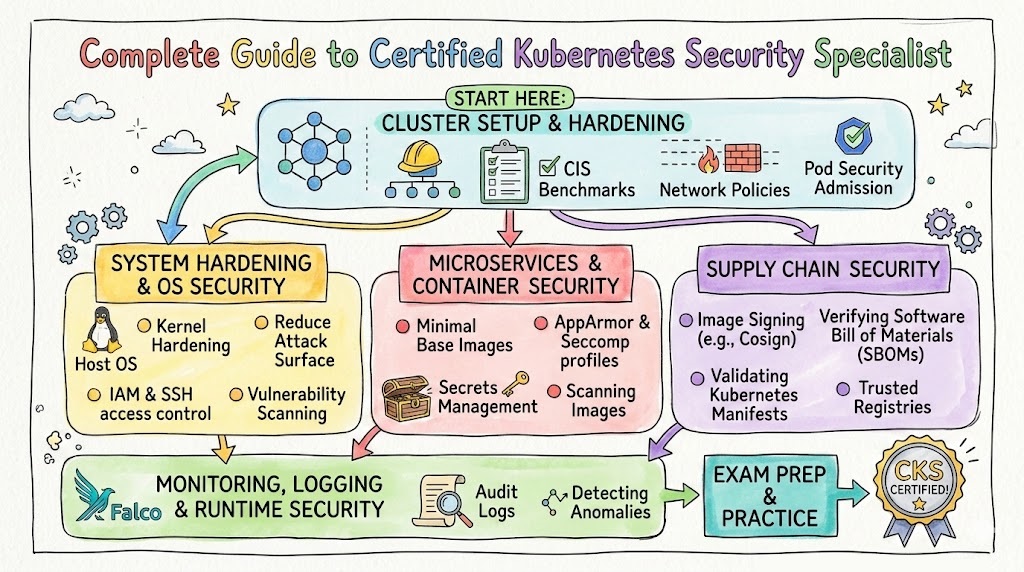
That is exactly why a Kubernetes security-focused certification matters. On the DevOpsSchool CKS page, the training scope includes areas such as cluster setup, cluster hardening, system hardening, minimizing microservice vulnerabilities, supply chain security, and monitoring/logging/runtime security.
For engineers, this means stronger hands-on skills.
For managers, this means lower risk, better compliance readiness, and better hiring signals.
What Is Certified Kubernetes Security Specialist (CKS)?
The DevOpsSchool page describes CKS as a professional certification for securing Kubernetes environments and explains that it is aimed at professionals responsible for Kubernetes security, including administrators and security specialists.
In practical terms, CKS is a specialization-level certification path for people who want to secure Kubernetes workloads and clusters in real production conditions.
It is not just theory. It is about doing the work:
- hardening access,
- reducing attack surface,
- managing secrets safely,
- improving image security,
- and detecting suspicious runtime behavior.
Who Should Read This Guide
This guide is useful for:
- DevOps Engineers who manage CI/CD + Kubernetes deployments
- SREs who need secure and reliable cluster operations
- Platform Engineers building internal Kubernetes platforms
- Cloud Engineers operating managed Kubernetes services
- Security Engineers expanding into cloud-native and container security
- Software Engineers deploying applications to Kubernetes
- Engineering Managers planning team skill development and certification roadmaps
DevOpsSchool’s CKS page also lists a broad target audience that includes Kubernetes admins, cloud admins, security engineers, DevOps engineers, SREs, developers, managers, compliance officers, consultants, and technical support engineers.
Certification Snapshot (CKS via DevOpsSchool)
From the DevOpsSchool CKS certification page:
- Course title shown: Certified Kubernetes Security Specialist (CKS) Certification Training Course
- Duration shown: 10–15 hours
- Training format shown: Online training / instructor-led live interactive sessions
- Certification type shown: Industry recognized
- Agenda coverage shown: cluster setup, hardening, system hardening, microservice vulnerabilities, supply chain security, monitoring/logging/runtime security
This aligns well with what working teams need today: practical Kubernetes defense skills, not only conceptual security vocabulary.
Certification Table
Below is a practical certification roadmap table centered around Certified Kubernetes Security Specialist and related progression options.
| Certification | Track | Level | Who it’s for | Prerequisites | Skills covered | Recommended order |
|---|---|---|---|---|---|---|
| Certified Kubernetes Security Specialist (CKS) | Kubernetes Security / DevSecOps | Advanced Specialist | DevOps, SRE, Platform, Security, Cloud engineers | Kubernetes basics + hands-on cluster use | Cluster hardening, RBAC, network policies, secrets, image security, runtime security | 1 (for this guide focus) |
| Master in DevOps Engineering (MDE) | DevOps + DevSecOps + SRE | Master / Comprehensive | Engineers, career switchers, managers building broader DevOps capability | General Linux/cloud/dev basics helpful | Broad DevOps, DevSecOps, SRE concepts and tools | 2 (cross-track broadening) |
| DevSecOps Certified Professional (DSOCP) | DevSecOps | Professional | Security-minded DevOps and platform teams | CI/CD + container + cloud basics | Security integration into SDLC, pipelines, controls | After CKS or parallel |
| SRE Site Reliability Engineering | SRE | Professional | SREs, ops engineers, platform teams | Linux, monitoring, scripting, systems thinking | Reliability, SLI/SLO, incident response, automation | After CKS for reliability depth |
| Certified Kubernetes Administrator (CKA) | Kubernetes Operations | Core/Professional | Admins, DevOps, platform teams | Kubernetes fundamentals | Cluster administration, troubleshooting, operations | Before or alongside CKS |
| Docker Certified Associate (DCA) | Containers | Foundation/Professional | Engineers working on containers | Docker/container basics | Container fundamentals, images, runtime, orchestration basics | Before CKS if container basics are weak |
| DevOps Certification (General track) | DevOps | Foundation to Pro | Working engineers and managers | SDLC and tooling exposure | CI/CD, automation, collaboration, delivery pipelines | Early roadmap |
| DevSecOps Certification (General track) | DevSecOps | Foundation to Pro | Security + engineering teams | DevOps basics | Shift-left security, controls, scanning, policy | After basic DevOps |
| SRE Certification (General track) | SRE | Foundation to Pro | Ops/SRE/Platform engineers | Monitoring + infra basics | Reliability practices, incident mgmt, automation | After DevOps basics |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
Certified Kubernetes Security Specialist (CKS) is a Kubernetes security-focused certification path for professionals who need to secure cluster infrastructure and containerized workloads. It is designed for practical, real-world security work in Kubernetes environments, including hardening, runtime protection, and supply chain awareness.
Who should take it
- DevOps Engineers working with Kubernetes in production
- SREs owning cluster reliability and incident handling
- Platform Engineers building internal Kubernetes platforms
- Cloud Engineers managing managed Kubernetes services
- Security Engineers moving into cloud-native security
- Software Engineers deploying services to Kubernetes
- Engineering Managers planning team security upskilling
Skills you’ll gain
- Kubernetes cluster security basics and risk thinking
- RBAC design and least-privilege access patterns
- Network policies and cluster-level traffic restrictions
- Secure ingress configuration and API access controls
- System hardening concepts for nodes and OS footprint
- Secrets management and safer workload configuration
- Container image hygiene and vulnerability scanning workflows
- Supply chain security awareness (registries, signing, validation)
- Runtime monitoring, logging, and audit log usage
- Incident detection and response thinking in Kubernetes
These align with the major agenda areas shown on the DevOpsSchool CKS page.
Real-world projects you should be able to do after it
- Design and apply namespace-level and app-level network policies
- Audit and fix over-permissive RBAC roles
- Harden cluster access paths and reduce API exposure
- Create a secure secrets handling workflow for app teams
- Build a basic image scanning gate in CI/CD
- Enforce a controlled registry allowlist for production workloads
- Configure runtime monitoring and audit logs for security visibility
- Review and improve pod security posture in existing deployments
- Create a Kubernetes security baseline checklist for your organization
- Run a tabletop incident response simulation for a compromised pod
Preparation plan (7–14 days / 30 days / 60 days)
7–14 Day Plan (for experienced Kubernetes users)
Best for: engineers already working daily on Kubernetes.
- Days 1–2: Review CKS domains and map your weak areas
- Days 3–5: Practice cluster hardening, RBAC, network policies
- Days 6–8: Work on secrets, workload security, pod configs
- Days 9–10: Practice image scanning and supply chain controls
- Days 11–12: Runtime security, audit logs, detection scenarios
- Days 13–14: Full mock practice and time-boxed labs
30 Day Plan (recommended for most working engineers)
Best for: DevOps/SRE/Cloud engineers with Kubernetes basics.
- Week 1: Kubernetes security fundamentals + lab setup
- Week 2: Cluster hardening + system hardening + access control
- Week 3: Microservice vulnerabilities + secrets + supply chain security
- Week 4: Monitoring/logging/runtime + revision + mocks + weak-area drills
Tip: spend more time typing commands and fixing broken configs than reading theory.
60 Day Plan (for busy professionals or managers transitioning hands-on)
Best for: software engineers, managers returning to hands-on work, or people from security backgrounds.
- Weeks 1–2: Kubernetes foundations refresh
- Weeks 3–4: Core CKS security domains with guided labs
- Weeks 5–6: Real-world scenario practice (RBAC, policies, secrets, runtime)
- Week 7: Mock exams + error analysis + speed improvement
- Week 8: Final revision + project-based consolidation
Common mistakes
- Treating CKS as a theory exam instead of a practical one
- Ignoring command-line speed and lab repetition
- Memorizing definitions but not practicing real cluster changes
- Skipping RBAC troubleshooting drills
- Not practicing network policies in realistic namespaces/apps
- Overlooking runtime security and audit logs
- Spending too much time on tools and not enough on fundamentals
- Not maintaining a personal checklist for hardening steps
- Cramming at the end without time-boxed practice
- Forgetting to review common misconfigurations
Best next certification after this
Best next (most practical):
- Same track: CKA (if Kubernetes admin foundation is weak) or a deeper DevSecOps certification path
Best next (career expansion):
- Cross-track: SRE certification for reliability + incident discipline
Best next (broader leadership/career planning):
- Master in DevOps Engineering (MDE) for a wider DevOps + DevSecOps + SRE roadmap (the MDE page presents it as a combined DevOps, DevSecOps, and SRE-oriented program).
What You Will Learn in CKS
The DevOpsSchool CKS agenda lists major security areas that form a strong Kubernetes security workflow.
Below is what those areas mean in practical project terms.
Cluster Setup Security
You learn how to secure cluster-level foundations:
- restrict cluster access using network security policies,
- review configurations using benchmark-based thinking,
- secure ingress objects,
- protect node metadata and endpoints,
- reduce unnecessary GUI exposure,
- verify platform binaries before deployment.
Why this matters:
Many teams try to fix app security first while the cluster base is still weak.
Cluster Hardening
You learn how to reduce exposure in the control plane and access model:
- restrict Kubernetes API access,
- use RBAC to minimize permissions,
- handle service accounts carefully,
- keep Kubernetes updated.
Why this matters:
A single over-permissive service account can become a major breach path.
System Hardening
You learn how to secure the node and host environment:
- minimize host OS footprint,
- reduce unnecessary IAM roles,
- reduce external network access,
- use kernel hardening tools (e.g., AppArmor/seccomp concepts shown in agenda).
Why this matters:
Kubernetes security is not only YAML security. Node and host controls matter.
Minimizing Microservice Vulnerabilities
You learn how to reduce risk inside workloads:
- manage secrets,
- apply OS-level security boundaries,
- use sandboxing approaches in multi-tenant cases,
- use pod-to-pod encryption concepts like mTLS.
Why this matters:
Microservice sprawl increases internal attack paths quickly.
Supply Chain Security
You learn to secure what enters your cluster:
- minimize base image footprint,
- whitelist registries,
- sign/validate images,
- use static analysis,
- scan for known vulnerabilities.
Why this matters:
If the image is already risky, runtime controls are only partial protection.
Monitoring, Logging, and Runtime Security
You learn to detect and respond:
- behavioral monitoring,
- threat detection across workloads,
- deeper investigation practices,
- container immutability thinking,
- audit logs monitoring.
Why this matters:
Prevention is not enough. You need visibility and response readiness.
Choose Your Path
This section helps different professionals decide how to place CKS in a larger career path.
1) DevOps Path
Goal: Faster and safer software delivery
Recommended sequence
- DevOps fundamentals / CI-CD basics
- Containers (Docker basics / DCA-type preparation)
- Kubernetes operations (CKA-type skills)
- CKS (Kubernetes security specialization)
- Broader DevOps/DevSecOps/SRE expansion (MDE or equivalent)
Best for
- DevOps Engineers
- Release Engineers
- Platform teams supporting multiple app squads
2) DevSecOps Path
Goal: Build security into delivery pipelines and platforms
Recommended sequence
- DevOps basics
- Security basics for cloud-native systems
- Kubernetes fundamentals
- CKS (hands-on Kubernetes security)
- DevSecOps Certified Professional (pipeline + SDLC controls)
Best for
- DevSecOps Engineers
- AppSec engineers moving to cloud-native
- Security champions in platform teams
3) SRE Path
Goal: Reliable, secure, observable platform operations
Recommended sequence
- Linux + networking + observability basics
- Kubernetes operations
- Incident response and reliability practices
- CKS (hardening + runtime visibility)
- SRE certification / advanced reliability path
Best for
- SREs
- Production support engineers
- Reliability-focused platform teams
4) AIOps / MLOps Path
Goal: Secure model/platform operations in containerized environments
Recommended sequence
- Python + data/ML workflow basics
- Containers and Kubernetes basics
- MLOps pipeline fundamentals
- CKS (secure model serving and platform runtime)
- AIOps/MLOps specialization and platform governance
Best for
- MLOps engineers
- Platform engineers supporting ML platforms
- AI platform teams working on Kubernetes
5) DataOps Path
Goal: Secure data pipelines and data platform workloads on Kubernetes
Recommended sequence
- Data engineering fundamentals
- CI/CD and infrastructure automation basics
- Containers + Kubernetes deployment basics
- CKS (secure data workloads, secrets, policies)
- DataOps platform and governance specialization
Best for
- Data Engineers
- Analytics platform engineers
- Data platform SRE/ops teams
6) FinOps Path
Goal: Cost-aware cloud operations with secure governance
Recommended sequence
- Cloud basics + cost concepts
- Kubernetes basics + resource usage understanding
- Platform governance and tagging/chargeback discipline
- CKS (secure access and compliance support)
- FinOps specialization with governance and operations optimization
Best for
- FinOps practitioners working with platform teams
- Cloud governance teams
- Engineering managers balancing cost + risk
Role → Recommended Certifications Mapping
Below is a practical mapping for the roles you requested.
| Role | Primary Recommendation | Secondary Recommendation | Why this combination works |
|---|---|---|---|
| DevOps Engineer | CKS | Master in DevOps Engineering (MDE) | CKS adds platform security depth; MDE broadens delivery + ops + security perspective |
| SRE | CKS | SRE Certification track | Strong fit for secure reliability, incident handling, and runtime visibility |
| Platform Engineer | CKS | CKA / MDE | Platform teams need secure multi-tenant Kubernetes operations + broad platform tooling |
| Cloud Engineer | CKS | MDE | Good for managed Kubernetes security plus broader cloud/DevOps operations maturity |
| Security Engineer | CKS | DevSecOps Certification track | CKS gives Kubernetes depth; DevSecOps broadens SDLC/pipeline security integration |
| Data Engineer | CKS | DataOps-focused training/cert path | Useful where data platforms run on Kubernetes and require secure workloads |
| FinOps Practitioner | MDE (broad operations awareness) | CKS (governance/security support) | Helps understand platform behavior, cost, access, and risk trade-offs |
| Engineering Manager | MDE | CKS (for platform/security team leads) | MDE supports strategic oversight; CKS helps lead Kubernetes-heavy engineering organizations |
Next Certifications to Take
You asked for 3 options in this format: same track, cross-track, leadership, and to refer to the DevOpsSchool Master in DevOps Engineering page. The MDE page positions itself as a broader program combining DevOps, DevSecOps, and SRE, which makes it a strong cross-track or leadership-oriented move after a specialist certification.
1) Same Track Option (Kubernetes / Cloud-Native Security Depth)
Recommended: Continue with Kubernetes admin and platform hardening depth (CKA-style skills + more real projects)
Why:
- CKS is strongest when paired with solid cluster operations depth
- Many real incidents are a mix of security + operational misconfiguration
- This improves your confidence in production troubleshooting
2) Cross-Track Option (DevSecOps Expansion)
Recommended: DevSecOps Certified Professional track
Why:
- CKS secures Kubernetes runtime and platform areas
- DevSecOps broadens your impact into CI/CD pipelines, SDLC controls, and shift-left practices
- This helps you move from “cluster security” to “end-to-end delivery security”
3) Leadership Option (Broader Architecture & Team Capability)
Recommended: Master in DevOps Engineering (MDE)
Why:
- The MDE page describes a combined DevOps + DevSecOps + SRE orientation, which is ideal for engineers growing into technical leadership and managers guiding platform teams.
- It helps with roadmap planning, team capability building, and cross-functional conversations
- Strong fit for Engineering Managers, Platform Leads, and Senior Architects
Preparation Strategy for Working Engineers and Managers
A common mistake is thinking certification prep is only for freshers. It is actually more useful for working professionals when done correctly.
For Working Engineers (Hands-On)
Focus on:
- daily lab practice,
- command speed,
- misconfiguration debugging,
- security reasoning under time pressure.
Use a “practice-first” ratio:
- 70% labs
- 20% review notes
- 10% mock / error analysis
For Managers (Hands-On + Planning)
Focus on:
- understanding what good Kubernetes security looks like,
- identifying team skill gaps,
- designing a phased learning plan,
- reviewing platform risk areas.
A manager does not need to become the fastest CLI operator, but should know:
- what to ask,
- what to review,
- and what a secure baseline should include.
For Software Engineers Moving to Platform Work
Your biggest wins:
- understand RBAC and service accounts,
- secrets management,
- network policies,
- image hygiene,
- secure deployment defaults.
This makes you much stronger than an app-only developer in cloud-native teams.
Common Career Outcomes After CKS
CKS does not magically change your career in one week. But it can make your profile much stronger when combined with real work.
What improves after CKS
- Better interviews for Kubernetes-heavy roles
- More trust in platform and production security tasks
- Stronger credibility in DevSecOps conversations
- Better understanding of incident prevention and runtime detection
- Better communication with security and compliance teams
Where it helps the most
- Startups scaling Kubernetes fast
- Mid-size companies formalizing DevSecOps
- Enterprises building internal platform teams
- Managed cloud environments needing stronger governance
What still matters beyond certification
- Project experience
- Incident stories
- Troubleshooting skills
- Clear documentation and communication
- Consistent learning
List of Top Following Institutions Which Provide Help in Training cum Certifications for Certified Kubernetes Security Specialist
DevOpsSchool
DevOpsSchool is a strong choice for learners who want structured, instructor-led support and a broader certification ecosystem under one provider. Its CKS page presents a clear topic-wise agenda and positions the training around practical security domains like hardening, supply chain security, and runtime monitoring. It is useful for working professionals who want guided preparation plus broader DevOps/DevSecOps/SRE growth paths.
Cotocus
Cotocus can be valuable for organizations and teams looking for implementation support alongside learning. It is often considered by professionals who want practical consulting exposure and problem-solving orientation, especially when training is tied to business use cases and delivery outcomes.
ScmGalaxy
ScmGalaxy is typically considered by learners exploring DevOps and automation ecosystems with a practical training-first mindset. It can be useful for people who want to strengthen fundamentals before moving into advanced Kubernetes security specialization.
BestDevOps
BestDevOps is often used by learners comparing certification and job-oriented technical training options. It may help candidates who want a structured curriculum, guided preparation, and training support while building toward cloud-native roles.
DevSecOpsSchool
DevSecOpsSchool is especially relevant for people who want a stronger security-first learning route. For CKS learners, a DevSecOps-focused environment can help connect Kubernetes security topics with CI/CD security, supply chain controls, and compliance-aware practices.
SRESchool
SRESchool can be a good fit for learners who approach Kubernetes security from a reliability and operations perspective. This is especially useful for SREs who want to improve runtime monitoring, incident handling, and production resilience while strengthening security controls.
AIOpsSchool
AIOpsSchool can support professionals working on intelligent operations, monitoring, and automation practices. For CKS candidates, it can complement runtime visibility and operational analytics thinking, especially in modern cloud-native environments.
DataOpsSchool
DataOpsSchool is relevant for engineers who run data platforms and pipelines on cloud-native infrastructure. CKS knowledge becomes more valuable when data services run on Kubernetes and need better secrets, access control, and workload isolation.
FinOpsSchool
FinOpsSchool is helpful for practitioners focused on cloud cost governance, optimization, and platform policy discipline. While FinOps and Kubernetes security are different specialties, they often meet in platform standardization, governance, and operational maturity conversations.
FAQ
1) Is CKS difficult for a working engineer?
It can feel difficult if your Kubernetes fundamentals are weak. If you already work with Kubernetes, it becomes much more manageable with focused lab practice and a clear preparation plan.
2) How much time does it take to prepare for CKS?
For experienced Kubernetes users, 2 weeks can be enough with disciplined practice. For most working professionals, 30 days is a safer plan. If you are switching roles, 60 days is a strong option.
3) Do I need to be a security engineer before starting CKS?
No. Many DevOps, SRE, and platform engineers take CKS to build cloud-native security depth. Basic security awareness helps, but hands-on Kubernetes experience matters more.
4) Is CKS useful for software engineers?
Yes, especially if you deploy applications to Kubernetes. It helps you understand secure deployment patterns, secrets handling, and production risks.
5) Should I do CKS before or after Kubernetes admin learning?
If your Kubernetes administration basics are weak, build those first or in parallel. CKS is much more useful when you can already work comfortably with Kubernetes resources and cluster operations.
6) Is CKS more useful than a broad DevOps certification?
They serve different goals. CKS is a specialist certification for Kubernetes security. A broad DevOps certification helps with end-to-end delivery, automation, and operations. Many professionals benefit from both.
7) Can managers benefit from CKS content even if they are not hands-on?
Yes. Managers can use CKS knowledge to define secure platform standards, evaluate team maturity, and ask better questions during reviews and incidents.
8) Does CKS help in DevSecOps roles?
Absolutely. CKS strengthens the Kubernetes/runtime/platform side of DevSecOps, which is a common gap in many teams.
9) What kind of projects should I build while preparing?
Build practical labs:
- RBAC hardening
- network policies
- secrets handling
- image scanning workflow
- runtime monitoring and audit logs
These are directly useful in real jobs.
10) Is theory enough for CKS preparation?
No. CKS-style learning is hands-on. You need repeated practice and troubleshooting, not only reading.
11) What is the best next step after CKS for career growth?
It depends on your goal:
- deeper Kubernetes/platform role → strengthen Kubernetes admin depth
- DevSecOps role → DevSecOps certification path
- team lead / broad role → Master in DevOps Engineering (MDE)
12) Does certification guarantee a job?
No certification can guarantee a job by itself. But it can improve your profile, credibility, interview conversations, and role fit when combined with practical projects and clear experience.
13) Is CKS valuable globally, or mostly for India?
It is useful in both India and global markets because Kubernetes security skills are relevant wherever teams run containerized production systems.
14) Can I prepare while working full-time?
Yes. A 30-day plan with 60–90 minutes on weekdays and longer weekend labs works well for many professionals.
FAQ
1) What is the main focus of Certified Kubernetes Security Specialist?
The main focus is securing Kubernetes environments across cluster setup, hardening, system security, workload risk reduction, supply chain security, and runtime monitoring/logging. These domains are reflected in the DevOpsSchool CKS agenda.
2) Who is the ideal candidate for CKS training?
DevOps engineers, SREs, Kubernetes administrators, cloud engineers, platform engineers, and security professionals who need practical Kubernetes security skills. DevOpsSchool also lists managers, developers, and compliance-related roles as beneficiaries.
3) How long is the CKS training course on the DevOpsSchool page?
The page shows a course duration of 10–15 hours.
4) What training format is listed for the CKS course?
The page shows online training and also describes instructor-led, live, and interactive sessions.
5) What are the most important skills to build for success in CKS?
RBAC, network policies, secrets handling, cluster hardening, image security, supply chain awareness, logging/audit visibility, and runtime security thinking.
6) Is CKS only for security teams?
No. It is highly useful for DevOps, SRE, and platform teams because they often own the Kubernetes environments where security controls must be implemented and maintained.
7) How should I balance work and CKS preparation?
Use a structured plan:
- short weekday practice sessions,
- longer weekend labs,
- weekly revision,
- and one final cycle of mock drills.
Consistency is more important than long study sessions.
8) What should I do after completing CKS?
Choose based on your goal:
- deepen Kubernetes operations skills,
- expand into DevSecOps,
- or move toward broader architecture/leadership with a DevOps + DevSecOps + SRE roadmap such as MDE.
Conclusion
Certified Kubernetes Security Specialist (CKS) is one of the most useful certifications for modern platform and cloud-native engineering teams because it directly improves how you secure real Kubernetes environments. It is not just a resume badge. It helps you think better, configure better, and respond better. If you are a working engineer, this can make you more trusted in production work. If you are a manager, it helps you build stronger teams and safer systems. Start with a practical study plan, focus on hands-on labs, and then choose your next step wisely—deeper Kubernetes, DevSecOps expansion, or a broader DevOps/SRE leadership path.